Why Zero Trust Security Matters to Your Organization
One important way of securing your organization against attacks and other cyber threats is to implement a Zero Trust security model for groups (distribution lists, security groups, Microsoft 365 groups) in on-premises Active Directory and Azure AD. After all, these groups control access to your IT assets, from sensitive data to vital communications channels and tools like Microsoft Teams and SharePoint.
A Zero Trust model requires never granting implicit trust but always verifying the legitimacy of access requests. So what does a Zero Trust security model mean for groups in Active Directory, Azure AD, and Microsoft 365?
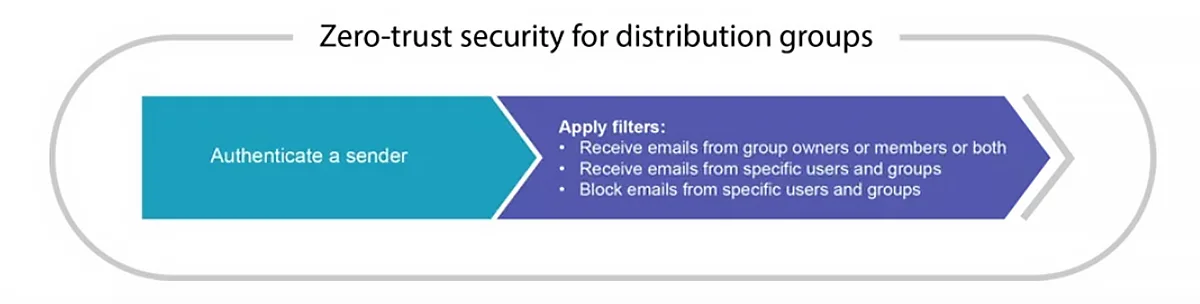
- For distribution groups, the rule solution is simple: authenticate, then filter. It is about not allowing delivery of messages unless they originate from a sender who can be authenticated and who has explicit permission to deliver messages to that group. It’s important to understand that attack methods involving distribution lists have evolved. In the past, threats usually involved including a malicious link or attachment in an email sent to the list. Today, attackers are focused on tricking user by disguising the identity of the sender and using social engineering.
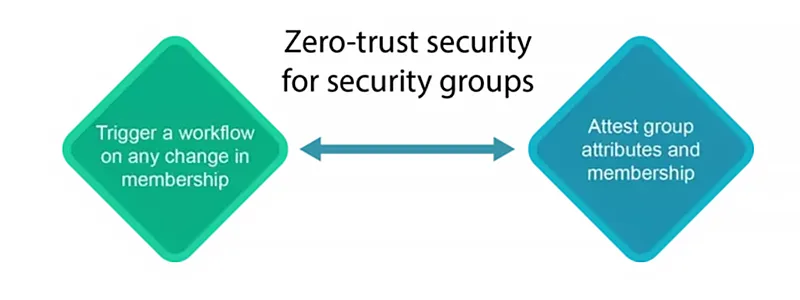
- For security groups, implementing Zero Trust is about preventing unauthorized users from altering group membership and rigorously enforcing the least-privilege principle by requiring group owners to regularly review group membership.
How to Implement Zero Trust Security using Netwrix GroupID
Netwrix GroupID offers a handy, yet powerful approach to implementing key Zero Trust best practices for distribution lists and security groups, and thereby reducing the risk from identity-based attacks. In particular, you can:
- Authenticate users who send email to a group.
- Control who can send email to a distribution list using whitelists and blacklists.
- Improve the accuracy of access decisions with dynamic group membership.
- Prevent improper changes to groups with auditing and approval workflows.
- Ensure groups have the right members and attributes through regular attestation.
- Accurately enforce least privilege with a thorough understanding of entitlements.
- Implement additional Zero Trust principles.
Authenticate users who send email to a distribution list
Netwrix GroupID helps you ensure that distribution list members receive email from trusted senders only. Simply enable the Require authentication to send mail setting in the group’s properties to block incoming emails from users who cannot be authenticated on the domain where the receiving group exists.
Control who can send email to a distribution list using whitelists and blacklists
To further help ensure that your distribution lists receive email only from trustworthy senders, Netwrix GroupID enables you to use both whitelisting and blacklisting. You can:
- Allow a distribution list to receive emails only from group owners, group members or both.
- Allow a distribution list to receive email from specific users and groups.
- Block emails from specific users and groups.
As a result, Netwrix GroupID treats all unknown domains, sending services, contacts, and other entities as untrusted — unless you grant permission.
Both authentication and filters are built into on-premises Exchange and Exchange Online; Netwrix GroupID’s magic lies in making these IT-oriented features easily available to group owners, who would otherwise likely remain unaware that these controls even exist.
Improve the accuracy of access decisions with dynamic group membership
Since security groups allow access to sensitive information and systems, it is imperative to that their membership be accurately assessed. But manual methods for updating group membership are slow and error prone.
To help, Netwrix GroupID offers dynamic group membership — you can build powerful LDAP queries to enable dynamic membership for your groups. You can schedule these queries to run automatically and update group membership whenever user information changes in the directory. For example, you can use dynamic groups to ensure that only current members of your IT team are members of security groups empowered to manage particular IT systems.
Netwrix GroupID offers an easy-to-use interface for building even complex queries. Simply specify the object type to be fetched by your query (such as group, user, or computer) and define the attribute criteria (such as department or location). You can augment the query further by specifying an external data source to be queried for matching records, and even write scripts to manipulate query results. As a result, you can ensure that the membership of even large groups is accurate while relieving the IT team from the burden of manually adding and removing members.
Prevent improper changes to groups with auditing and approval workflows
Any improper change to a group’s membership can endanger both productivity and security. Netwrix GroupID helps mitigate this risk with auditing and approval workflows. You can set up a workflow that monitors a particular attribute of a specific user or group for certain change events (add, edit or delete), and automatically sends those events to a designated user for approval or denial.
In particular, you can define workflows that control changes to a group’s LDAP query that defines its membership. Netwrix GroupID’s history tracking function also logs all changes to group attributes and membership.
Ensure groups have the right members and attributes through regular attestation
Regular group attestation is essential to ensure that each user can access only the IT resources they need to do their job. In particular, it helps you identify groups that have members who should no longer be part of the group and groups that have outlived their purpose.
Netwrix GroupID enables you to force group owners to review their groups and either make changes to them or attest that they are correct and current. Owners can easily review the following for their groups:
- Membership— Members can include both users and nested groups.
- Permissions— A group’s permissions should be limited to those that group members need to accomplish their tasks.
- Attributes — Examples include the group’s description, email address and expiry policy.
- Purpose — Groups that are not needed for a defined business purpose should be deleted or disabled.
Accurately enforce least privilege with a thorough understanding of entitlements
Zero Trust helps protect your data and systems from unauthorized access. Therefore, you need to have a clear understanding of all entitlements to your IT resources, such as file servers and SharePoint sites.
Netwrix GroupID makes it easy to gain this understanding. You can:
- Discover all domain-joined file shares
- Analyze the permissions on each folder and file
- Uncover cascading entitlements from inheritance
With this deep insight, you can establish and enforce least privilege, which is a core best practice for a Zero Trust security model.
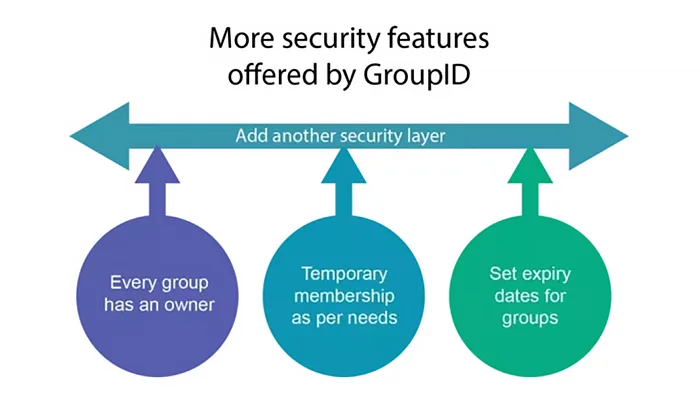
Implement additional Zero Trust principles.
Netwrix GroupID can empower you to implement many other aspects of Zero Trust, such as:
- Identify orphaned groups — Groups that have no owner are a serious security risk, since no one is responsible for ensuring they have the right membership and permissions, or even attesting that they serve a purpose.
- Grant temporary group membership — Members in an Active Directory, Azure AD or Microsoft 365 groups can be automatically added and removed for a temporary period.
- Set expiry dates for groups — Having groups automatically expire reduces the risk from groups outliving their intended purpose.
Security – Today and Tomorrow
Adopting a Zero Trust model is vital for both security and business continuity. A great way to get started is to gain control over the groups that grant access to your IT resources. Netwrix GroupID can help you secure your Active Directory, Azure AD and Microsoft 365 groups — and therefore the data and applications they provide access to, from your file shares to email to SharePoint and Teams.