I admit to being a big fan of Centrify so I was especially pleased to find this “chalktalk” they were giving on the same day that I was researching Group Based Access Control (GBAC). The premise of my research was that Role Based Access Control (RBAC) is too limiting, trying to fit a square user into a round role — there is only so much granularity you can get with roles. Active Directory security groups are a better way to manage access and permissions in my opinion.
Centrify’s solution is for managing access to UNIX, Linux and OS X through Active Directory and specifically leveraging Active Directory groups. Wow, that is right up our alley! We manage AD groups dynamically, creating dynamic security groups and distribution lists. We also give very granular control over end user AD self service so that you can trust your users to manage their own AD groups. It seems like a perfect fit, certainly more automated than managing these groups through Active Directory Users and Computers (ADUC).
Having these two solutions together makes for a seamless and simple way to manage UNIX, LINUX, and OS X but I’m still struggling to find a company that does GBAC for Windows users. I must be missing something; I know that Windows provides the capability natively with GPOs but every single other major component of the AD infrastructure has a 3rd party software that takes Windows functionality and makes it simpler and more robust, why not GBAC? There are a million RBAC solutions, even some Attribute Based Access Control vendors but no 3rd party Group Based Access Control softwares.
I’m still in the beginning stages of my research but somehow we are going to make it easier for organizations to manage access through AD groups. It just makes too much sense not to.
Jonathan Blackwell
View ProfileSince 2012, Jonathan Blackwell, an engineer and innovator, has provided engineering leadership that has put GroupID at the forefront of group and user management for Active Directory and Azure AD environments. His experience in development, marketing, and sales allows Jonathan to fully understand the Identity market and how buyers think.

The challenge with GBAC is that it creates an auditing nightmare. RBAC provides a relationship between the Role, the Rights it grants, and the Resource so you can easily see the consequences of adding someone to a role. IT is almost impossible to say what the consequences are of adding someone to an AD group, especially when you expand their usage out to foreign systems and applications. GBAC’s inability to provide this link and to restrict the rights a group can convey are its fatal flaw.
Patrick Parker
Product Manager
The Dot Net Factory
There have been several attempts at providing the Enterprise with RBAC controls, which I believe is the right way to solve access control and privilege management challenges. However, I agree with Edward that that it would be easier to gain IT adoption of an RBAC solution if they were provided with tools that allowed them to control the assignment of users into specific Roles. At Centrify, we’ve adopted this management model of using AD groups as a way to assign specific users to a Role which then further grants a specific set of UNIX/Linux access permissions as well as Privileges… Read more »
David, I agree completely that groups are easier to use as a proxy for role assignment given the ubiquity of the ADUC/ADAC user interface. In a perfect world ;-), all applications would support external authorization. Our approach has been to provide an ADUC/ADAC style that makes it easy to manage using roles. The RBAC system then uses “controlled” AD groups only when necessary to grant ACLs. The RBAC system maintains the relationships of who has access to what and even adds this capability for the AD groups making the auditors happy. For applications that do not require groups for permissions… Read more »
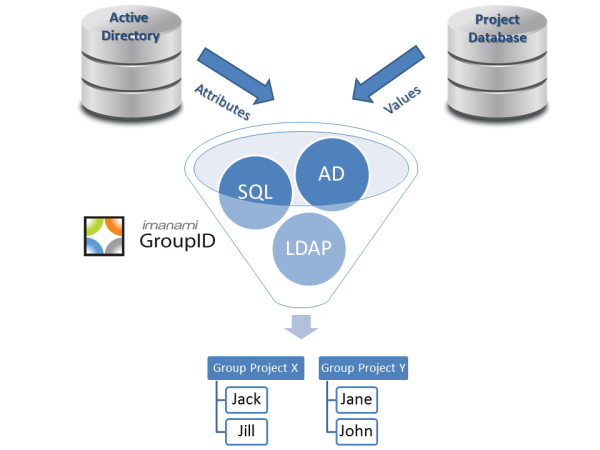
Patrick, I agree with you to an extent but it’s more of an issue with the lack of current tools than with the concept of GBAC. Centrify has a great first step to making this concept of GBAC work, we are about to have an excellent proof of concept in the marketplace that shows how this will work. Just because you can’t currently match a group’s access to the group doesn’t mean that we never will be able to. Security groups are ubiquitous, even organizations using roles use SGs as well. What is missing is that tool that does the… Read more »
That last sentence put a smile on my face 🙂 That is our goal with EmpowerID – to unite the power of RBAC with the practicality of groups. Screenshot of this in action: http://bit.ly/acctEJ
Patrick Parker
The Dot Net Factory