Because of the lack of attention groups get throughout their lifetime, one of the greatest security risks an organization faces is when a group lives too long. Think about it – you have groups that exist today that, despite having a clear understanding of the logic behind its membership, you have zero idea why it’s there or what it provides access to. Even worse, you likely have a number of groups with no members, giving you zero context of why the group exists.
In many ways, the ever-living group is the culmination of a number of group management sins – no certifying of members, no certifying of permissions, possible repurposing of existing groups, and renaming groups. If all these administrative “no-nos” occur, over the years upon years a group continues to exist past its intended lifespan, it has incorrect members and waaaaay too many permissions.
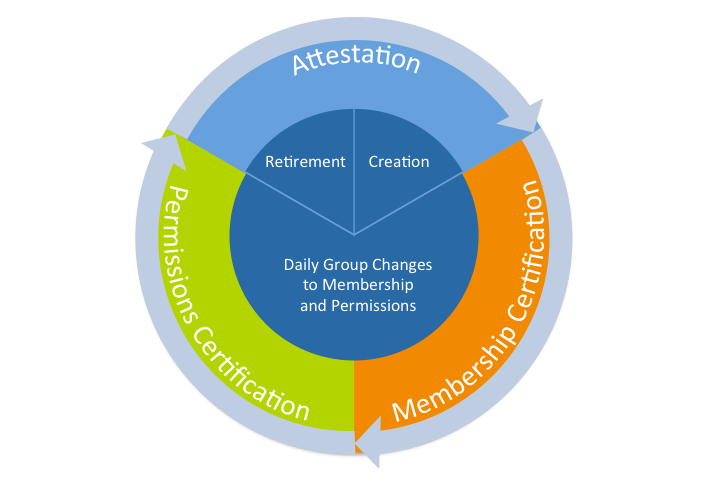
In this last blog of a four-part series on creating proper AD Group Lifecycle Management, we want to look at the cradle and grave parts of a groups’ life, and see how attestation plays a role in maintaining proper group security.
The issues I raised above bring to light the need to know whether a group should exist or not. To accomplish this, you need to have the following two steps in place:
- Assign a group owner – this is different from the ownership around membership and permissions (which I covered in my last two blogs). Here, you need an owner that is responsible for the group from creation to deletion. More than likely, this can be the same owner who certifies members – the department head, application owner, or line of business owner. Since they are closest to the actual use of the group by users, it makes sense that they would know when the group is no longer needed by the organization.
- Periodically Perform Group Attestation – At least quarterly, this owner should go through a process of attesting to IT that the group is, in fact, still necessary – and what its purpose is.
This attestation helps in two ways:
- At the end of a group’s life – If a group is no longer needed, or if its usefulness will be expiring soon, the owner should notify IT, so that deletions of the group can be scheduled.
- Prior to group creation – because attestation includes informing IT of the groups purpose, IT has a reference to check to see if a group already exists that meets its need, rather than following the traditional path of simply creating yet another group.
The attestation of groups keeps AD clean and, more importantly, secure by making certain on the needed groups (and the associated access they grant) exist to meet the current business needs.
Putting the Lifecycle Together
I’ve covered the three major tenets to the AD Group Management Lifecycle, shown below.
Your next step is to begin to build a process of defining the one or more owners of each group, establishing the IT processes that keep owners in the loop, and instituting a recurring process of certification and attestation.
Jonathan Blackwell
View ProfileSince 2012, Jonathan Blackwell, an engineer and innovator, has provided engineering leadership that has put GroupID at the forefront of group and user management for Active Directory and Azure AD environments. His experience in development, marketing, and sales allows Jonathan to fully understand the Identity market and how buyers think.