In many organizations, Active Directory provisioning consists of a series of manual processes and emails and help desk calls that ultimately finish with an employee having a network login and hopefully an Exchange email account. It is ripe with potential for errors and just not a good use of limited resources.
But then the problem gets exacerbated in the next step. Giving a person an offer letter moves them from person to employee. Provisioning an Active Directory account turns that employee into a user. To move them from user to “productive user” requires access to resources, something that often requires group membership.
That’s why I find the traditional definition of provision and deprovision to be so limiting. What organization wants a user with an AD user account only? So that user can sit at their desk and type their password and possibly browse the web (assuming that right isn’t controlled by a security group)?
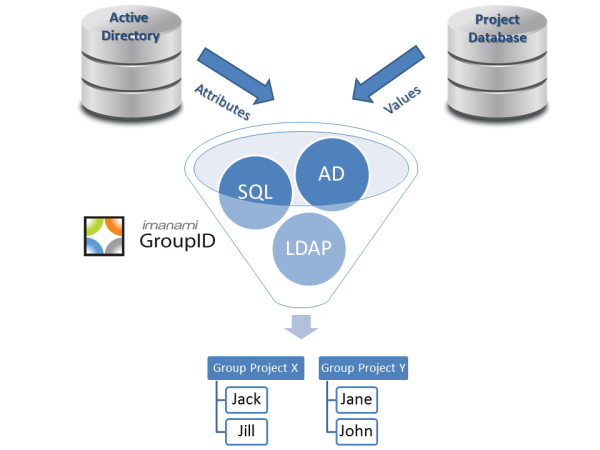
Provisioning really needs to extend to the next logical step, AD security groups and Exchange distribution lists; thes group memberships should be automated. If someone is in the Albuquerque office, they should be in the groups associated with that office. If they are in marketing, they should be on the correct DLs and security groups. Automatically.
This gives the whole middle part to a user’s life in between provisioning & deprovisioning. Access to resources and information. And it’s very easy to accomplish.
Unfortunately, that’s the point that Imanami’s involvement ends currently. We provision/deprovision users into Active Directory and Exchange. And then we automate all of those users’ group memberships. Other, more expensive, IdM suites do solve another problem…getting users provisioned into other systems. Think about keycard systems, parking passes, security certificates and anything else that the user needs. This is fundamental to provisioning and something of which we are keenly aware.
But the first step has to be to get rid of the “Rube Goldberg” approach, ditch the manual processes, and automate the AD provisioning to the point of productive user immediately.
Jonathan Blackwell
View ProfileSince 2012, Jonathan Blackwell, an engineer and innovator, has provided engineering leadership that has put GroupID at the forefront of group and user management for Active Directory and Azure AD environments. His experience in development, marketing, and sales allows Jonathan to fully understand the Identity market and how buyers think.


Much the same thing said very well here by Dave Kearns.