Years ago, I heard a stat that the average user gets provisioned into 16 directories when hired and deprovisioned from only 10 directories when leaving. For the math challenged, that leaves the ex-user active in 6 directories. Which is, of course, a problem.
Today’s IT infrastructures are big and complex and there are lots of nooks and crannies for users’ identity data to hide in. IT might not even realize how some of it got to where it was. This makes deprovisioning a user even more important.
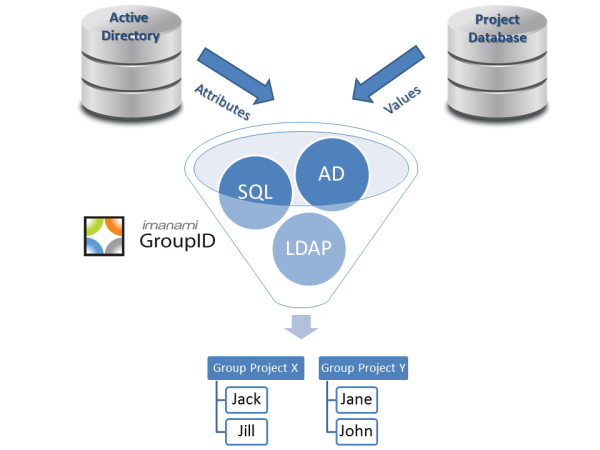
The obvious route to take is to have a directory synchronization tool that can delete user objects out of each and every directory or database (or set them to inactive, or change the password, or logically delete them, or disable them or expire them). But this is assuming you know all of these databases and directories.
At Imanami, we advocate this approach with one extra safety valve. Security groups, get these users out of each and every security group that they were in. By doing this, you add an additional barrier. If the user somehow can get into the network, they won’t have access to anything. This is an additional case for having a strong group management solution: if you are granting access to resources and systems with security groups, then taking a user (or ex-user) out of those security groups now denies them access.
You can read more about how Imanami manages dynamic Active Directory security groups, take a look at our chalk-talk, or contact us for a demo. If you want to deprovision your Active Directory users completely, get them out of the groups.
Jonathan Blackwell
View ProfileSince 2012, Jonathan Blackwell, an engineer and innovator, has provided engineering leadership that has put GroupID at the forefront of group and user management for Active Directory and Azure AD environments. His experience in development, marketing, and sales allows Jonathan to fully understand the Identity market and how buyers think.