According to the 2015 Verizon Data Breach Investigations Report, approximately 85% of data breaches are performed by an external threat actor, with approximately 45% of those breaches focusing on credentials. This makes sense. Without proper credentials, the threat actor won’t be able to access the target data they want.
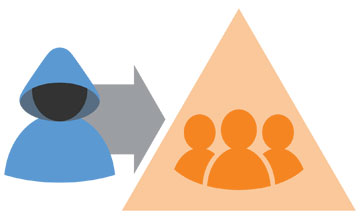
Most threat actors gain entry by phishing, malware infection, or social engineering in order to gain control over an initial endpoint. Once they get this access, their next step is to determine both the credentials that the now-compromised user has and what the user has access to.
For example, an attacker may perform a number of common tasks in an effort to attain elevated privileges, such as counting the groups that the current user belongs to or enumerating the local group memberships (such as Local Administrators). Once local administrator privileges are attained, tools such as mimikatz can be used to extract plain-text passwords, hashes, and kerberos tickets from memory.
And for every account accessed in this manner, the next step is frighteningly simple: enumerate the groups that each set of credentials belongs to. The threat actors use these stolen credentials to access additional resources, starting the process all over again. This cycle continues until the attacker obtains the right set of credentials that grant them access to the data they are seeking.
So, what does this have to do with groups? In a word: Everything.
In a recent blog, we saw that organizations are validating neither group memberships nor the permissions assigned to those groups on a regular basis. This infrequent monitoring of the state of security via Active Directory groups is exactly what is enabling and empowering these attackers.
Think about it: If you continually add members to groups, and add permissions, but never certify that the current membership and permissions are correct, you’re simply granting more and more permissions to users, potentially giving attackers more and more access to systems and resources.
Some of you may think this just isn’t the case in your Active Directory. But in reality, users across many organizations — no different from your own AD users — report that they have too much access and that IT isn’t implementing strict controls to enforce least privilege.
Therefore, it may be time to embrace the likelihood that you have some really bad group management habits, accept the reality of external threats to organizations today, and realize how much the intersection of the two puts your organization at risk.
Jonathan Blackwell
View ProfileSince 2012, Jonathan Blackwell, an engineer and innovator, has provided engineering leadership that has put GroupID at the forefront of group and user management for Active Directory and Azure AD environments. His experience in development, marketing, and sales allows Jonathan to fully understand the Identity market and how buyers think.
