Everyone’s worried about endpoints. And you should. As evidenced by the rise in organizations experiencing attacks via malware-laden websites, phishing and spear phishing, and OS/application vulnerabilities, the endpoint is a clear target for external attackers. Compromising an endpoint is frequently the first step needed to gain a foothold within your organization’s network, giving these attackers a beachhead from which to spread out laterally to other endpoints and, eventually, to the system that gives them access to valuable protected data.
However, before the attackers can get their greedy little hands on your company’s data, they need to accomplish a few things:
- Get that initial access: This is where the malware, phishing, social engineering, etc. all come into play. The attacker needs one of your users to become an unwitting participant in the attack by running an attachment app, opening a Word doc with a macro, or visiting a website with hidden code that takes advantage of a browser.
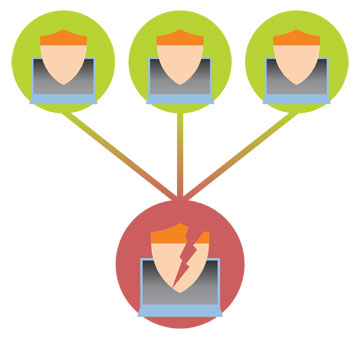
- Establish a foothold: To create a foothold, the attacker must figure out which sets of credentials will give them a higher/elevated level of access so that they can extend their reach.
- Spread out laterally: Once attackers have gained access to that “foothold” endpoint, they use credentials to compromise and exploit additional endpoints.
- Repeat: In many cases, attackers know what kind of data they are looking for (e.g. social security numbers in an HR database), but they have no idea about which system is housing that data. So they need to continually and repeatedly access multiple endpoints in the same manner again and again until they can identify, locate, and access the endpoint that gets them to the desired data.
To prevent this from happening, you need a layered defense. No single solution, process, policy, or task is going to put a stop to the ever-changing threat represented by external attacks. Your defense needs to include:
- Mail security: Every organization needs a solution that searches through email for potential malicious intent — and prevent users from interacting with it.
- Application black/white listing: Defining which applications are allowed to run, while simultaneously denying all others, is a strong approach to keep malware and maliciously-used tools from running on an endpoint.
- User training: Users need to be made aware of the prevalence and potential havoc these attacks can have on your organization, so keeping them informed can help keep you organization as vigilant as possible.
- AD group management: Because the threats are constantly changing, your security position should be one that assumes that even with a layered defense, someone will still get in and use information about group membership to identify their next target. By properly managing groups, their permissions, and their membership, you limit the amount of inappropriate permissions that exist today in your organization, keeping the attacker from easily gaining access to the protected data that you never want them reaching.
The first three parts to your defense are important: They will keep the majority of attackers at bay and not let them in. But it’s not enough to simply put up walls between you and the attacker, assuming they’ll never build a ladder and climb over. A strong defense assumes that attackers will get in and has plans to limit where attackers can go after they do get in. Cnce an attacker is within the walls of your company, only proper group management can protect you.
Check out the whitepaper, The Role of AD Group Management & Self-Service in Your Security Strategy, to learn more about how AD group management helps create a stronger security stance.
Jonathan Blackwell
View ProfileSince 2012, Jonathan Blackwell, an engineer and innovator, has provided engineering leadership that has put GroupID at the forefront of group and user management for Active Directory and Azure AD environments. His experience in development, marketing, and sales allows Jonathan to fully understand the Identity market and how buyers think.