As your organization has grown, so has your IT infrastructure. You now have so many systems requiring some level of authentication, and so many protected data sets that need to be protected, that your organization has come to the realization that it’s time: You need to implement IAM. At first, this can be an exciting proposition. Thoughts of how great security will be start to fill your head — single sign-on, two-factor authentication, application control, audit trails, etc. To a security geek, it sounds glorious.
But there’s just one problem.
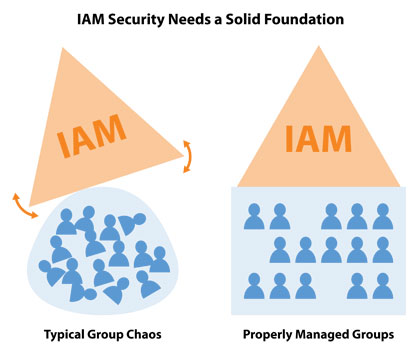
All of those IAM capabilities (that are truly cool, for the record!) are all based on a single common assumption: you already have secure measures in place. Think about it for a minute. Users log in with advanced authentication… only to be given access via application control… which is based on established security privileges. And what’s the basis for those privileges? Active Directory groups.
While you’re probably excited about jumping in and starting to implement the cool new IAM tech, you may be getting ahead of yourself. After all, adding those new features on top of group membership-based access that has largely gone unmanaged over the years — and that is potentially insecure at its core — may not be the wisest course of action.
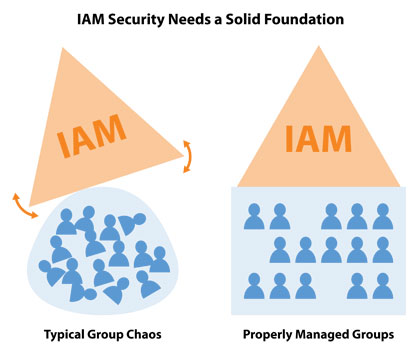
Accordingly, you need to start IAM by first asking yourself, “are my groups and their security actually secure?”
Because it’s very likely that a large percentage of your users have too much access with your current security configuration, there are two basic Active Directory group management tasks that you need to perform prior to implementing IAM:
- Validate Group Security: There are many questions that you need to know the answers to before group security can be considered acceptable:
- Are the permissions assigned to a given group correct?
- When is the last time anyone reviewed them?
- Do they provide too much access? Too little access?
- Do the application access needs possibly require dividing a group into smaller groups in order to provide more granular access?
- Validate Memberships: This is probably the more likely culprit that is allowing users to have too many permissions. Users are frequently added to a group, but these memberships are rarely managed beyond that. Before moving forward, you need to determine whether the memberships are correct. If not, should users be removed?
To validate both of these issues, you should seek the input of users who are closer to the group’s purpose. For example, if a group provides access to the Accounts Payable system, talk to the AP supervisor and/or the VP of Finance. Ask them about whether the memberships are up to date and what access those users need in order to get their job done (which you can translate back to the security level granted to the group).
Build IAM on a Solid Foundation: Groups
Implementing IAM is all about providing better security. However, in most cases, the foundation of that security is a set of groups that no one has touched in years. So it’s critical that you first spend a little time organizing your Active Directory groups and their security. A simple cleanup is a solid first step, but IAM itself will evolve and change over time, just as your business’s needs do.
Further, while you can start with getting groups in shape, you may also want to begin thinking about how to leverage business stakeholders and implement an Active Directory group management strategy that keeps your group-based security current.
Jonathan Blackwell
View ProfileSince 2012, Jonathan Blackwell, an engineer and innovator, has provided engineering leadership that has put GroupID at the forefront of group and user management for Active Directory and Azure AD environments. His experience in development, marketing, and sales allows Jonathan to fully understand the Identity market and how buyers think.