Ensure Right People with Right Access to Right Information at Right Time
Defining system access for employees can be a challenging task for organizations of all sizes. But unless intimate knowledge of each employee’s role is known, granting access is often cumbersome and demands manual input from the IT department. What is needed is an automated way to identify and define roles across the organization, and automatically grant access based on that role’s needs. For many companies this is much easier said than done.
Defining roles through criteria is not new. Companies categorize employees as follows:
- Department
- Job Title
- Location
- Rate of pay
- Rank
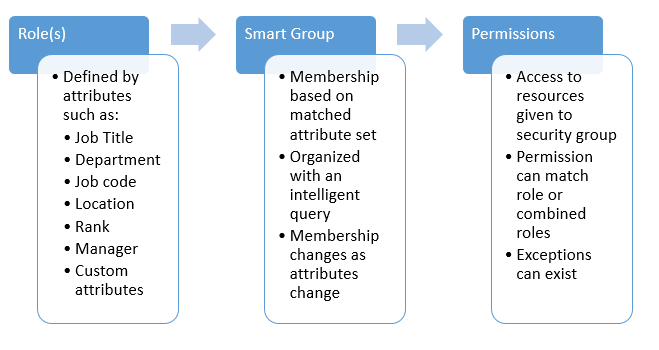
And while this criterion is valuable for HR and IT for various uses, it can also be leveraged and put to practical use to define resource access without the need for manual access management. The challenge in automating access management lies with scale. How can a global organization automate resource access management? In a report by Anna Forrester, United States Air Force CTO Frank Konieczny has uncovered the solution in a common-yet-overlooked place—attributes.
“It’s based on attributes for each individual in a sense that as soon as the person’s attributes change, their role changes and we automatically authenticate for particular access to data or particular systems.”
Achieve Access Automation on Scale
This is a simple method of automating access on scale, and it is highly accurate. Access is based on the collection of attributes assigned to roles, and as the roles and employee assignments change, so will the attributes. This allows ongoing automation of access throughout the employee’s career at the organization without the need for constant human intervention. An automated program can instead manage ongoing demands of employee access management, with corporate security not left to chance or subject to human error.
The process today is very familiar:
- Attributes for each employee are stored in a directory.
- Roles are defined as a collection of attributes.
- As the attributes for employees change, the changes are reflected across roles.
- Permissions are granted to specific groups in a directory.
- As roles change, a manual request is made to alter employee access.
- A request might be made to remove an employee who no longer needs access. (Note: Removal is dependent on a manual change by a human, and thus security is compromised until—or if—the change is made.)
Benefits of Access Automation on Scale
With automation, the process is vastly improved, and security is not compromised as follows:
- Membership in groups that grant access are not based on static lists but are based instead on a set of rules or criteria that define the role(s) of who should be included.
- As roles change, it is automatically reflected in role attributes.
- Membership is now managed through software instead of humans. The software is continuously monitoring for any changes in attributes and automatically adjusts the membership accordingly.
These automated tasks ensure immediate access to the right resources as roles change. These same automated tasks also ensure timely security changes by regularly removing people from access they no longer need to be a part of as reflected in their attribute changes. Best of all: All of this is accomplished without human intervention.
Important Note: Attributes often exist in more than just your directory service. For example, if an organization needed to evaluate directory attributes and also needed to query against an ERP (or other type of database system) where more sensitive information might reside, it would need to establish intelligence for evaluating group membership on an additional resource. It is crucial that the software selected is capable of leveraging a public set of attributes as well as a system where confidential attributes can be cultivated for determining membership in groups.
Conclusion
When it comes to managing groups in your directory, automating based on attributes that represent unique roles is key to ensuring ongoing accuracy and truly a best practice for those concerned with security. This is a trademark of Imanami’s flagship Automate product. A solution from a company with more than a decade experience focused on this unique task.
Some organization have attempted to solve this problem with either brute force but archaic methods such as scripting, and custom programs. Or they try to get a monolithic apparatus do something that was meant for other more global tasks.
These projects always seem to fail because the experience required to successfully implement and maintain such sophisticated solutions always requires more domain knowledge in this discipline than is readily recognized. Usually it is better to buy a tool purpose-built for the task with hundreds of users who have proven the technology than it is to reinvent something to do something that is just too important to leave to chance with unproven methods and means.
Jonathan Blackwell
View ProfileSince 2012, Jonathan Blackwell, an engineer and innovator, has provided engineering leadership that has put GroupID at the forefront of group and user management for Active Directory and Azure AD environments. His experience in development, marketing, and sales allows Jonathan to fully understand the Identity market and how buyers think.