I am constantly reminded how ubiquitous Active Directory groups are in our everyday corporate lives. They are seemingly used for everything (they’re not just for email any more).
To illustrate, let me tell a quick story. One of my colleagues wasn’t able to finish a project as he was working from home. He told me he couldn’t VPN in to get some documents he needed. I scrunched up my face in that “lame user error” sort of way and patiently explained how easy VPN’ing is.
I figured that the next time he tried, it would work thanks to my expert coaching. Fast forward a couple of days and I’m looking at our AD self service solution, GroupID. It turns out I’m a member of some group called “access from home.” I take a quick look at the members of this security group and see that aforementioned colleague wasn’t in this group. I tell him to join the group (it had a workflow but he got approved) and bingo, he could VPN into the network now!
 OK, so how do you make this work? Turns out it’s simple. We have ISA Server which has Firewall, Proxy Server and VPN server capabilities. We’ve enabled the VPN server and ISA is a member of our domain.
OK, so how do you make this work? Turns out it’s simple. We have ISA Server which has Firewall, Proxy Server and VPN server capabilities. We’ve enabled the VPN server and ISA is a member of our domain.
To specify a domain group of users for which remote access is allowed. We go to Virtual Private Networks (VPN) node in ISA Server MMC and Click Configure “VPN Client Access”. On Groups tab, we added the Access from Home group and clicked OK. That’s all.
 The cool part is that we are using our own product to manage that group. We have it set up as a mail enabled security group set to a security setting of “semi-private.” What that means is that if a user attempts to join the group, it will trigger a workflow that has to be approved by the owner(s) of the group. In this case, it is the office manager.
The cool part is that we are using our own product to manage that group. We have it set up as a mail enabled security group set to a security setting of “semi-private.” What that means is that if a user attempts to join the group, it will trigger a workflow that has to be approved by the owner(s) of the group. In this case, it is the office manager.
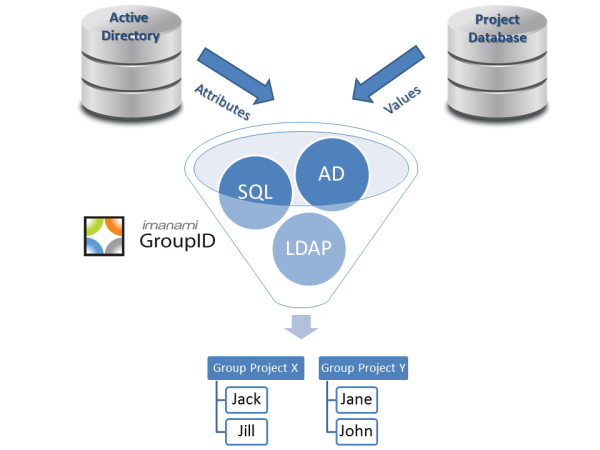
We could also make it a dynamic group if we wanted and set a query against a flag in either the HRIS or Active Directory. In some organizations, the query could be that if their office address is not an official company location. It is a great way to use Active Directory groups to make your organization more productive. And secure.
Jonathan Blackwell
View ProfileSince 2012, Jonathan Blackwell, an engineer and innovator, has provided engineering leadership that has put GroupID at the forefront of group and user management for Active Directory and Azure AD environments. His experience in development, marketing, and sales allows Jonathan to fully understand the Identity market and how buyers think.