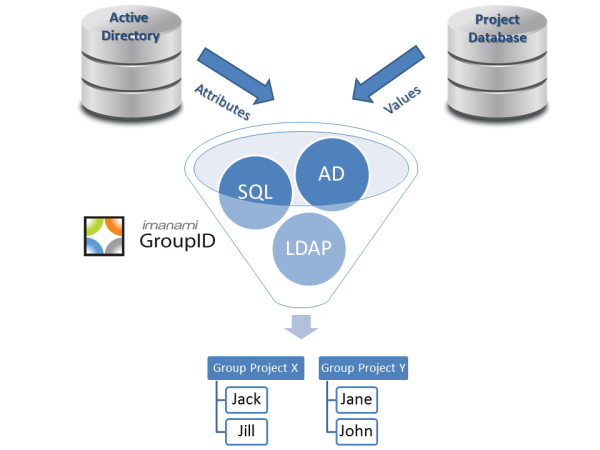
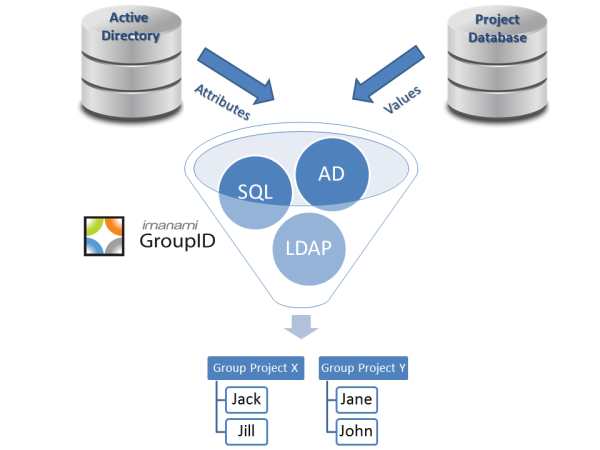
In role based access control, security groups and distribution lists will by design, have specific associations to resources based on the need to apply a certain job function, task, or action to specific classifications of workers. The membership of security groups and/or distribution lists are adeptly managed using object attributes stored in Active Directory with role based group membership products like Imanami’s GroupID. In fact, we have a blog that speaks of group membership based on AD attributes. With the roles based on Active Directory attributes, membership of these groups is handled very well.
What about those people for whom Active Directory attributes are not enough to define their role?
There are some use cases where a company has designated roles for which there is no applicable attribute in Active Directory and there is no desire to apply that data into Active directory nor is there a desire to extend the Active Directory schema to hold these external data attributes. For this, many companies who have employed project style databases for which information is time sensitive and highly transitional may extend group membership criteria to these other sources of information.
Imanami recognizes that leveraging external data sources such as an ODBC data source, Microsoft SQL Server, Oracle databases, and foreign LDAP directories can dramatically extend the usefulness of Smart Groups by employing information that might not otherwise be available in the Active Directory meta verse, but pertinent to the function in which the group in which members is assigned. Some example use cases:
Use Case 1:
A manufacturer of special widgets has put together an engineering and a marketing team to develop and promote its new wares. During the development phase, it has identified a set of employees with “Engineer” in their job description working out of one of their development labs located in Denver. Using Imanami’s GroupID Automate, an IT administrator has created a mail-enabled security group with membership based on the employees with the AD title attribute containing “Engineering” and the office location attribute containing “Denver”. Further, the IT administrator filters the membership by connecting to a SQL database which is tracking the development phase of the new wares and verifies that amongst the engineers, they are also currently active in the project by ensuring that only those engineers in the critical path and active between milestone dates are included in the lookup. The group is scheduled to be updated automatically every day, ensuring that only those being added to the project and matching the filter are included and those who leave the project are removed from the group. All done with the customizable group membership based on the needs of the project itself.
Use Case 2:
An educational institution has already leveraged GroupID Synchronize to dynamically provision and de-provision students based on class enrollment database(s).
They have also used GroupID Automate to assign faculty and students to appropriate security groups and distribution lists based on the attributes in Active Directory – i.e., role based assignments. What they also have are project/lab related activities whereby additional security groups and/or distribution lists need to be assigned based on more transient needs. This information is not stored in the enrollment database, but in a separate database tracking those activities. Leveraging this additional business knowledge, GroupID Automate can assign those faculty and students as members of the groups necessary for their success.
Use Case 3:
A business with a subset of its employees maintaining strong ties to union labor management has a need in which local unions leaders can quickly disseminate information to their union constituency on the workforce. Human Resources does not track who are active members of the union and that information is not replicated into Active Directory. There is however, a database of union membership that is a subset of the employees. Leveraging connectivity to this external database, GroupID Automate is able to filter membership only to those who are active in their respective union and in a specific location.
As with attributes in the Active Directory schema, external data sources can be leveraged in many scenarios to build membership in groups that uniquely fit the needs of your organization. With regular updates to the membership handled automatically, your organization is always assured of having the most flexible and sometimes complex needs for group membership handled intelligently.
We would love to hear from you and learn of additional example use cases for this type of group membership flexibility leveraging not only Active Directory attributes, but external data sources as well.
Download our Free Whitepaper:
Unleash the Power of Active Directory Groups
Jonathan Blackwell
View ProfileSince 2012, Jonathan Blackwell, an engineer and innovator, has provided engineering leadership that has put GroupID at the forefront of group and user management for Active Directory and Azure AD environments. His experience in development, marketing, and sales allows Jonathan to fully understand the Identity market and how buyers think.