Just as Active Directory has a user object for each network user, it has a computer object for each computer in the domain. These objects are treated as an account. As with user accounts, computer accounts provide a means for authenticating and auditing the computer’s access to the network and its access to domain resources. Each computer to which you want to grant access to resources must have a unique computer account.
Computer objects have the following purposes:
- Computer objects are security principals. This means that just as with user objects, you can give permissions for resources and assign security group memberships to the computer.
- A computer account ties the workstation or server to the Windows security model.
- A computer object is a placeholder for properties that help you when you are remotely installing and managing workstations.
- A computer object is a placeholder for properties that are purely informational.
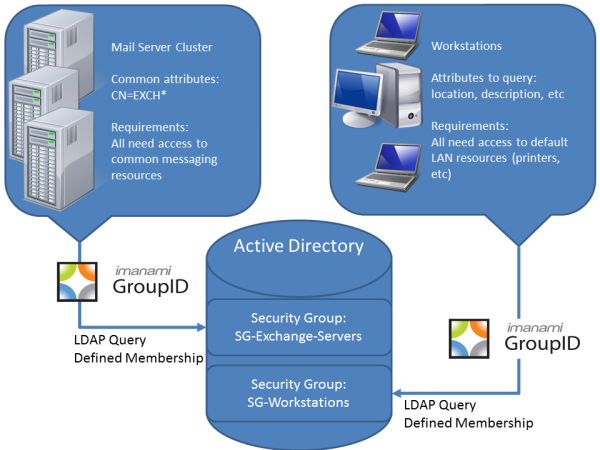
Computers can be assigned to security groups as members. These security groups can then be delegated access to domain resources. With group nesting, computers can then inherit from parent groups, the security access granted to those resources. Managing computer access can be a challenging aspect of any administrators work.
Typically, file servers, mail servers, workstations, mobile laptop computers and more will be identified with specific information about the location, purpose or use of the asset. For many, these are valuable as informational details for tools such as auditing.
These attributes become even more valuable as you leverage them to determine the purpose and role of that computer asset and apply security rights based on those roles. With those determinations, the business can establish criteria for security group membership. Leveraging a tool such as Imanami’s GroupID Automate, you can intelligently group your computer resources into security groups with automatic membership provisioning as new computer resources are attached to the domain.
Contact an Imanami GroupID consultant to discuss the benefits of automating group membership for your Active Directory computer and your user objects.
For a free demo of GroupID contact us at sales@imanami.com
For more information about how Group ID can automate the manual processes of managing security groups and distribution lists, download our free whitepaper by pressing the button below:
Unleash the Power of Active Directory Groups
Download Whitepaper
Jonathan Blackwell
View ProfileSince 2012, Jonathan Blackwell, an engineer and innovator, has provided engineering leadership that has put GroupID at the forefront of group and user management for Active Directory and Azure AD environments. His experience in development, marketing, and sales allows Jonathan to fully understand the Identity market and how buyers think.

