Most large corporations use Microsoft Group Policy Objects (GPOs) to force a signature onto employees’ email. Usually it is a bit of legal mumbo-jumbo (that is the technical term, laymen may use something more descriptive) that states that you had better be the correct person that this email was sent to and it’s not our fault if we typed the email address wrong. You’ve all received those.
But in multi-national corporations (and even companies Imanami’s size can be multi-national), how do you account for language differences? What if you need a different level of warning based on a person’s job title? What if there are differing legal implications based on department? Or what if you don’t want customer facing positions to have as harsh of a message?
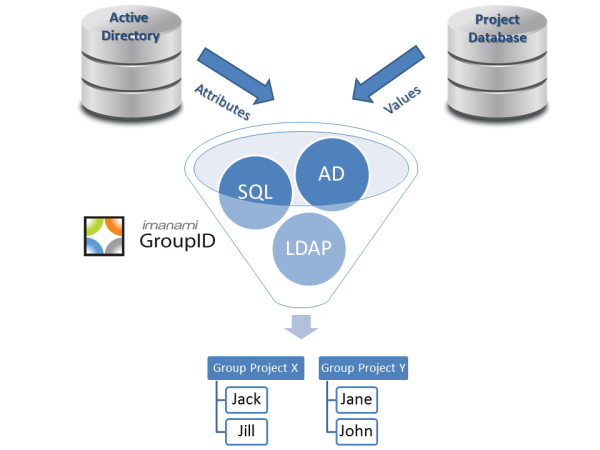
It ceases to be as simple as putting different country’s employees in different OUs and applying the GPO based on that. You need to start using Active Directory groups, the more dynamic the better, as you can be assured of accuracy that way. One of our customers (actually an analyst firm that should be pointing this out to all of their clients) employ a two layer dynamic security group to apply these signatures to: the first layer is country to determine language and the second is based on department to determine the legal severity of the message.
These have to be dynamic security groups since you cannot filter group policy settings based on distribution lists. The reason that they need to be dynamic is that you want to make sure that EVERYONE who fits these criteria are in the group as soon as they fit these criteria.
It is important that there not be any holes in the Active Directory group membership for any employees as they won’t get a signature. If you cannot employ an active directory reporting tool to figure this out, you will need to have a default GPO that will apply a default signature to anyone not covered by the security group GPO filter.
Disclaimer: This blog post is intended solely for the recipient to whom I meant to address it and I am in no way responsible for you reading it if I did not intend for you to browse to it. If you have read this blog post in error, please notify me immediately and destroy any memory you have of this blog post.
Jonathan Blackwell
View ProfileSince 2012, Jonathan Blackwell, an engineer and innovator, has provided engineering leadership that has put GroupID at the forefront of group and user management for Active Directory and Azure AD environments. His experience in development, marketing, and sales allows Jonathan to fully understand the Identity market and how buyers think.