David Bell wrote an interesting piece in Secure Computing on how to avoid flaws in Identity Management. The part that I really liked was how he pointed out that the IT security industry is focusing its efforts on “where” enterprises keep their critical data instead of “who” has access to it.
 It is this “who” that causes the problem. The thing is you can lock up data to the point where nobody can see it and, voila, it is secure. But there are still users in the organization that need to see and/or use the data. So you grant them access and all is right with the world. Until they leave the company or change jobs or departments. Here’s the big problem, these users still usually have access to the data. You gotta solve the “who”.
It is this “who” that causes the problem. The thing is you can lock up data to the point where nobody can see it and, voila, it is secure. But there are still users in the organization that need to see and/or use the data. So you grant them access and all is right with the world. Until they leave the company or change jobs or departments. Here’s the big problem, these users still usually have access to the data. You gotta solve the “who”.
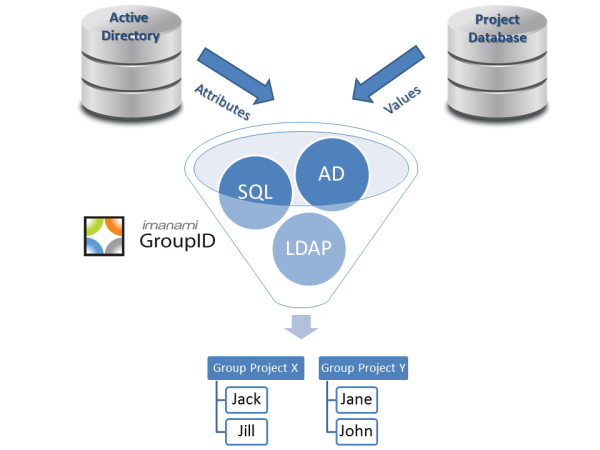
We already know that 93% of organizations use Active Directory security groups to grant access to resources and/or systems. Between deprovisioning ex-employees and managing these security group memberships, this is where most of the organizations fail on the “who” equation.
Over 80% of organizations use some variation of manual processes to manage Active Directory security group membership. Do you think that those manual processes are going to catch every single user who goes from marketing to sales? Or worse yet, operations to sales? Suddenly you have sales reps with access to the tools that can control orders or pricing. This is more dangerous than how you encrypt those tools. (It’s not just sales, they’re just easy to blame for things).
My recommendation to avoiding these flaws in identity management? Solve the low hanging fruit, make your major AD security groups dynamic. If somebody changes departments or titles, they’re going to not only get their new access but have their old access taken away. Quickly and without IT having to initiate a manual process.
Avoiding the easily solved flaws will keep major long term flaws from happening.
Jonathan Blackwell
View ProfileSince 2012, Jonathan Blackwell, an engineer and innovator, has provided engineering leadership that has put GroupID at the forefront of group and user management for Active Directory and Azure AD environments. His experience in development, marketing, and sales allows Jonathan to fully understand the Identity market and how buyers think.