I just read a great article by Rick Vanover called, Windows security groups: To nest or not? He asks the question because a nested security can be a bear to troubleshoot if you start getting quirky permissions issues.
In the article Rick states, “I would love to say that nesting group membership is prohibited, but there are occasional situations where it makes sense. My professional administration practice has limited nested group membership with a few guiding rules”
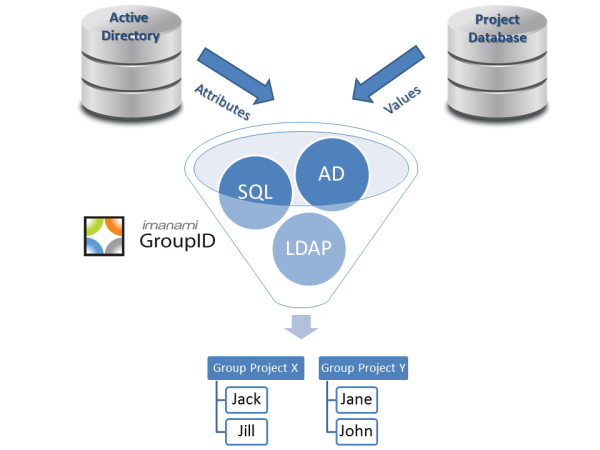
And this makes sense, there are very valid reasons to nest Active Directory groups but you need to make sure you have controls in place to keep it from getting out of control. Having the guidelines in place is helpful but if you have mutliple admins or help desk personnel working in ADUC (and many many companies have this situation), these rules can get overlooked.
For GroupID Self Service, we have created a help desk role that gives help desk permissions to manage user and group objects with controls in place as to what they can change, create, expire or delete. That way you can give them the tools they need to do their job that is more than an end user can do and less than what an Admin can do.
The control that is most pertinent to the nesting issue is our group hijacking workflow. Basically, if you try to nest a security group or distribution list into another group, the owner of the groug being nested (nestee?) needs to approve it. That way the group won’t start getting unwanted email or suddenly have permissions being applied to it that the group owner doesn’t want.
Following smart guidelines like those described in the article AND having the tools in place to help ensure guideline compliance will allow you to have a safely structured nested Active Directory group structure without the troubleshooting nightmare.
Jonathan Blackwell
View ProfileSince 2012, Jonathan Blackwell, an engineer and innovator, has provided engineering leadership that has put GroupID at the forefront of group and user management for Active Directory and Azure AD environments. His experience in development, marketing, and sales allows Jonathan to fully understand the Identity market and how buyers think.

Getting approvals will not solve the problem. The problem isn’t just nesting … it’s also that security groups are used on myriad locations making it difficult to determine who has access to what. The requirements in an AD design of group membership should be to attain the following: 1) given a user I can determine every resource that user has access to 2) given a resource I can determine all users who have access (and what type of access (read/modify/etc) 3) given a user/resource, I can determine why the user has access To do this with nesting, follow these rules:… Read more »
Mark,
Thanks for the comment. I’m trying to think of ways that we can make role groups even easier. If you have any ideas that you would like to see, please feel free to email me at edward.killeen@imanami.com .
I will certainly credit you when I blog about this topic!