Managing Active Directory groups is probably one of the simplest tasks you perform on a regular basis. It’s right up there with resetting a password. Because it takes little effort — and even less though — it can often be easily dismissed as a routine, unimportant task.
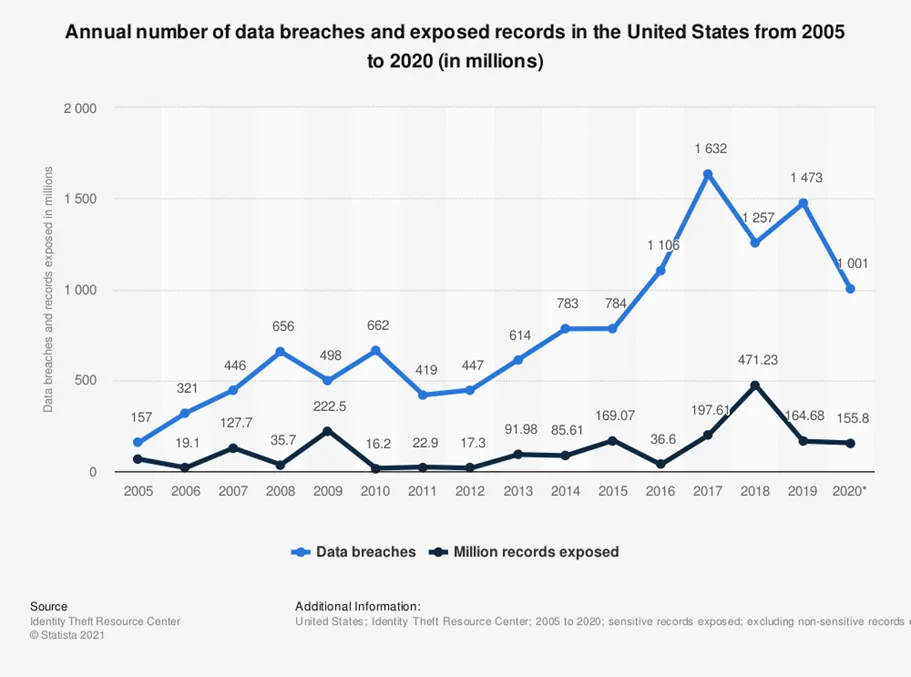
Similarly, administrators must regularly clean up user accounts and objects to help ensure optimum performance and network security. Although Active Directory uses encryption, poor active directory cleanup procedures can leave organizations exposed to cyberattacks and can result in costly data breaches.
Managing Active Directory Groups: The Challenges
During a webinar for Imanami, we asked the audience to provide some anecdotes about the challenges they have faced when managing Active Directory groups. Here are some of the repeating themes we uncovered, along with a few quotes from IT pros just like you:
Security Crisis Created by Lack of Management
Groups are the pathway to provide access to the internal network, Active Directory, applications, and data. A lack of attention will lead to disaster.
Scenario: “We have several groups that still have disabled users in them as well as users who no longer work for the company. We have groups that don’t have ownership or any description of what the group does. I’m actually in the middle of a huge Active Directory cleanup.”
Think about the likelihood for a breach: there’s with no clear understanding of why groups even exist, and some groups contain with users who are no longer employees, this is a Russian hackers dream. This reminds me of a story about an IT admin who was fired but had created a backdoor account for himself before leaving, because he had suspected that he would be fired. After being terminated, he logged in and wreaked havoc for his former employer.
The scenario above shows how easy it is for bad actors to infiltrate your systems. Nest a few groups that link all the way to the Domain Admins and perhaps to the VPN access group and place a seemingly benign user account in one of these nested groups — bingo. Someone has external access, and you may be updating your resume.
According to a survey, 58 percent of respondents stated that cyber security policies and procedures (and documentation) is included as one of the components for cyber security risk assessments in their organizations.
Active Directory Group Graveyards
Without any kind of documentation or determination of who is responsible for managing a given group, groups become a security risk. And because no one is exactly sure if there will be a negative impact by deleting this group, the groups simply remain in existence. This is the wrong type of welcome mat.
Scenario: “We have too many groups. We have over 1,100 groups with no members alone.”
And this IT pro hasn’t even addressed issues such as whether any of these groups are nested, what resources they have access to, etc.
Read more: Active Directory Token Bloat & Group Glut
Too Many Hands in the Active Directory Soup
The number of users with privileged access in Active Directory should be as limited as possible. Often, it’s easier to simply give someone Admin rights either to the domain or to one or more OUs. When you add to that a lack of documenting why groups exist and where they provide access to, you have a recipe for disaster.
Scenario: “Too many IT folks have access to modify groups without understanding their purpose. And we have no auditing of Active Directory object changes to track them.”
This is a trifecta of Active Directory group management problems:
- Too many people.
- No idea how changes in membership will impact the organization.
- No ability to see who is modifying what.
Changing Your Active Directory Management Reality
The examples above are only three of the themes mentioned. If any of these resonate with you, it’s time to change how you implement AD group management. A shift in thinking is required. Groups must be seriously regarded to access everything within your organization. Group management needs to shift from being that thing you do to close a helpdesk ticket to being seen as a task that has the potential to cause serious problems if not handled correctly.
As organizations grow, the number of active users (both internal and external) may expand at an alarming rate. The number of user accounts in Active Directory can quickly reach beyond what administrative employees can manually accommodate. In larger organizations and enterprises, IT departments will need to rely on automated Active Directory maintenance to avoid writing custom scripts every time. Process automation accelerates the cleanup process, minimizes human error, and helps ensure adherence to best practices.
If you’re interested in learning more about the right way to manage Active Directory groups, then check out What’s the Right Way to Manage Groups in Active Directory?
GroupID solves for all Active Directory Management Challenges
Maintaining appropriate oversite of groups is critical to ensure that a group does not outlive its purpose – and should be expired and deleted when no longer needed. Delegation with fine-grained control is the key. GroupID is a comprehensive, out-of-the-box solution recognized as the top Active Directory Group Management tool. IT professionals from companies like Splunk, Nvidia, Samsung, Toshiba, Disney, and FedEx prefer GroupID among the top applications. GroupID has the highest-rated technical support as well.
GroupID by Imanami offers a suite of solutions that empowers IT professionals to manage groups, users, and entitlements effectively and automatically. Learn more about the suite of solutions under GroupID here.
Jonathan Blackwell
View ProfileSince 2012, Jonathan Blackwell, an engineer and innovator, has provided engineering leadership that has put GroupID at the forefront of group and user management for Active Directory and Azure AD environments. His experience in development, marketing, and sales allows Jonathan to fully understand the Identity market and how buyers think.

