Let’s admit it! Active Directory health check is a challenge – no matter the company size.
Symptoms of Poor Active Directory Health
The first indication that your organization’s Active Directory isn’t healthy is when a flood of calls comes to the help desk indicating a potential crisis is brewing. Active Directory works okay even when it isn’t 100 percent healthy. But this usually aids in hiding problems that should be fixed by IT staff who are busy putting out other fires.
Other symptoms of poor active directory health that become part of the routine if not addressed include:

If you were to do a search on the web for “Active Directory health,” you’d find countless articles on how to verify the “health” of your Active Directory environment. Most contain references to checking domain controllers, AD-related services, replication, DNS, and DHCP — all to assess whether Active Directory is working correctly or not.
Correct Usage of Services for Active Directory Health Check
The degree to which an AD environment remains healthy revolves largely around the services being provided. We compartmentalize Active Directory into two parts: the core services that Microsoft provides and the configuration that IT pros implement within Active Directory. If the core services are running as expected, we say that Active Directory is healthy. However, this is only part of the story.
Shouldn’t the health of Active Directory also consider whether those services — authentication and access — are being provided correctly?
Much of the correctness of Active Directory services relies on proper configuration being put in place by IT — from topology to security and everything in between. Some of these parts, like security, might seem to be farther away from the core services, but an improper security configuration is still reflected in the overall services that Active Directory provides: The wrong security leads to the wrong service being provided. Therefore, we respectfully submit that the true health of your Active Directory relies on the security configuration of your Active Directory.
Is the security within your Active Directory healthy?
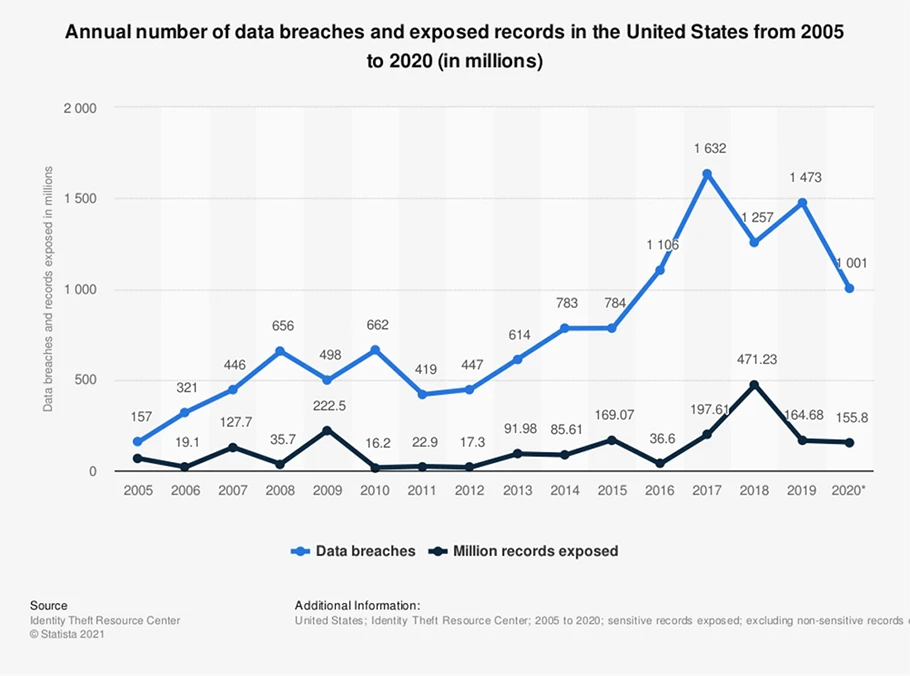
In 2020, the number of data breaches in the United States came in at a total of 1001 cases. Meanwhile, over the course of the same year over 155.8 million individuals were affected by data exposures – that is, accidental revelation of sensitive information due to less-than-adequate information security.
As organizations and their security needs have grown over time, the reliance on outdated Active Directory management technology has remained static. So, what should you be looking at to ensure that the security within your Active Directory is healthy?
There are a few other parts of Active Directory that should be considered when determining the overall “health” of AD:
- The state of your permissions: Active Directory permissions are one of those parts of managing AD that simply take on a life of their own — and rightfully so. Permissions to external resources aren’t stored within AD objects, so you likely have users and groups that are heavily over-permissioned. Knowing what permissions are assigned to which objects would provide you with a more valid and more complete sense of security.
- The state of your group memberships: Like permissions, no one pays much attention to group memberships once they’ve been created. Given that these objects are likely the primary means of assigning permissions, they deserve equal attention.
- The state of groups: After a time, some groups probably shouldn’t even exist anymore: Their usefulness ended months or years ago, yet they still continue to exist, complete with members and permissions.
- The state of AD management: This is not referring to Active Directory administration — you know, the daily changes needed here and there to put out the latest fire. This refers to the true management of your Active Directory’s security, groups, and memberships. If you do not have a formal process that, at a minimum, reviews the current state of the first three items in this list, you’re not truly managing Active Directory. You’re simply addressing the latest helpdesk ticket.
Read more: Uncovering the Risk in Your Security
Measurement and Analysis
Monitoring is key to easily identifying and understanding the causes of availability, replication, security, and other Active Directory performance issues. Your concern about the health of your Active Directory health is warranted — Active Directory represents the foundational service on top of which reside every other application and some access to resources. But you can’t just stop at monitoring the replication between two DCs. Health must also include how Active Directory is configured to provide services, specifically security.
Go over the finer points of Active Directory Health Checks, recognize issues, understand errors, and remediate issues you discover in your Active Directories. To get a better picture of the overall health of your Active Directory environment, check out Imanami’s free online diagnostic tool, Health Meter.
Jonathan Blackwell
View ProfileSince 2012, Jonathan Blackwell, an engineer and innovator, has provided engineering leadership that has put GroupID at the forefront of group and user management for Active Directory and Azure AD environments. His experience in development, marketing, and sales allows Jonathan to fully understand the Identity market and how buyers think.

