Defining identity management exactly is an interesting question. In many ways the definition is completely different from organization to organization and vendor to vendor. Wikipedia (the authoritative source of collective watered down wisdom) says:
Defining identity management exactly is an interesting question. In many ways the definition is completely different from organization to organization and vendor to vendor. Wikipedia (the authoritative source of collective watered down wisdom) says:
Identity management is a broad administrative area that deals with identifying individuals in a system and controlling access to the resources in that system by placing restrictions on the established identities of the individuals.
That’s pretty good. Basically, it’s knowing who people are and what they can do. It misses some of the intricacies of making it easier for people to do what they need to do based on who they are, but you can infer it. But that’s also where a lot of IdM solutions fail — making it easier for people to do what they need.
You really want to make sure that an HR Manager in Topeka can do everything that an HR Manager in Topeka should be able to do from day one in that position. Also, you want to make it easy for that HR Manager in Topeka to be a little different than others if he/she needs slightly different access (my main gripe against roles).
But to get there, you need to make sure that you really know that this person is an HR Manager in Topeka. It sounds silly but if you don’t know the person’s title and department and location in your directory, you cannot possibly assign them the correct role or security group memberships. And if you don’t get them in the correct role or group right away, that HR Manager in Topeka can’t access anything they need.
Identity Management fails immediately without these important steps. The problem is that IdM solutions are so vast and all encompassing that these basic most important steps are often overlooked or not given the attention they need. I can’t tell you how many prospects laugh nervously when asked how accurate Active Directory is for them.
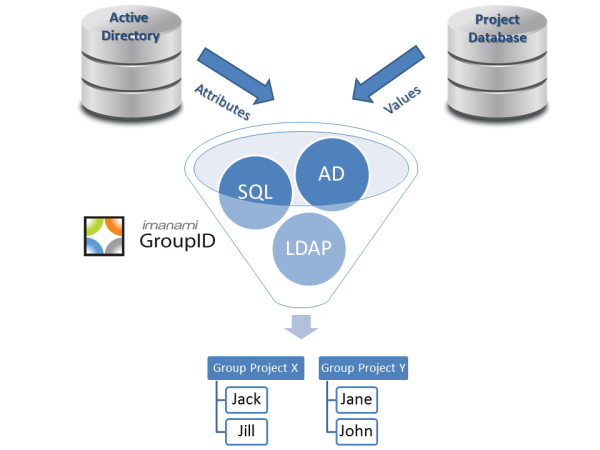
This idea of fixing the most basic and important step in Identity Management has greatly colored Imanami’s definition of it. GroupID’s whole raison d’etre is to make sure these steps get done and that you know exactly who your user is and know for absolute certain that they are in the right security groups. And IT can do it with no manual intervention.
Check out GroupID and see if you start defining Identity Management the way we do.
Jonathan Blackwell
View ProfileSince 2012, Jonathan Blackwell, an engineer and innovator, has provided engineering leadership that has put GroupID at the forefront of group and user management for Active Directory and Azure AD environments. His experience in development, marketing, and sales allows Jonathan to fully understand the Identity market and how buyers think.