Managing Active Directory (AD) is not an easy task, but someone has to do it. If this “someone”, is you, then you should always keep in mind that human beings make mistakes and have bad habits, even if they are AD gurus.
To minimize the risk of such bad habits from happening on your watch, we’ll walk you through the most common ones and help ensure that you avoid them as a routine.
Why is it important to keep your Active Directory healthy and secure?
Keeping your AD secure is important. Proper upkeep of your Active Directory is crucial to cybersecurity because Active Directory holds the keys to the proverbial kingdom. With the ability to assign and enforce security & encryption protocol, control the storage & flow of data, and manage access rights, certificates, and security roles, AD is truly the core of the entire IT infrastructure.
Read more: 3 Steps to Gaining Control and Governance over Permissions
It’s been said that admitting that you have a problem is the first step on the road to recovery. So, let’s all take a deep breath, and say it together: My groups are a mess. Come on… we know you can do it.
Don’t believe your groups are a mess?
Let’s take a look at the 7 bad habits that IT typically has when it comes to managing groups in Active Directory. How many apply to you?
-
Set it and Forget it!
We’ve all done it — made a group, added some users, gave it permissions, and moved on to put out the next fire. The problem is this: you have probably never gone back to that group ever again, which turns a forgotten asset to the organization’s security into a forgotten gap in security.
-
Don’t Document!
How many of us have bothered to fill in the Managed By tab? Or completed the Notes field to document the origin of the group and who is responsible for it? The likely answer “not many of us.” Without properly documenting this information, there’s no ability for IT to understand why a group was created, whether it needs to continue to exist years after its creation, and how one group can be differentiated from another.
-
Make Changes without Context
Typically, when your helpdesk receives a request to add a new group member, assuming that the requestor checks out, the helpdesk team just goes ahead and makes the change. Do you even ask yourself the following?
- Is that even the right group to be modified?
- Are the permissions given to that group appropriate to the person being added? Remember, you probably have no documentation to verify this.
- What access is being granted?
Without the proper context around a group’s purpose and the permissions assigned, it’s difficult to ensure that security is properly maintained.
-
Make Changes without Accountability
Continuing with the previous example, who is verifying that the changes being made are appropriate? By itself, a request does not provide sufficient justification. It’s likely that the helpdesk team doesn’t check with the appropriate person to validate the request: anyone higher up the ladder in IT, someone closer to the application being granted access to, or even a line of business owner. Without some level of accountability, your helpdesk is simply helping your groups become an even bigger mess.
-
Keep IT the Owner
When you created the group, you never set the Managed By values because you just figured IT would manage the group. However, as discussed above, this approach does not provide the context needed. Accordingly, it may be a good idea to designate someone closer to the resources being granted access to as the group “owner” (even if only for the purpose of later reference). This provides a way for IT to reach out to the right people when change requests are made to understand the context and address accountability issues.
-
Don’t delete anything… EVER
Most organizations have no group membership management process that includes the removal of members and groups. If this sounds familiar, you probably have groups with members or permissions to resources (or both) that you don’t even remember that they exist! Think about that for a moment. There are users with access to resources — of whom IT isn’t even aware. Not good!
-
Do it all yourself
As discussed previously, you probably never go back and manage groups: clean them up, verify that memberships are correct, confirm that the permissions assigned are necessary, etc. Therefore, they’re a mess in the first place.
It just doesn’t make sense to have IT be the owner of a group. Someone much closer to an application — who knows which staff should be using an application, what permissions they require, etc. — should be the one to manage a group’s membership, approve permission assignment, and even verify whether a group remains necessary or can be deleted.
We’re all in the same boat
If you are like most IT professionals, you are probably guilty of at least half of these bad habits — or more. Don’t feel bad. The question is, what can we do about it?
What’s the next step?
After admitting that there may be a problem, the next step is identifying the problem. For some of you, you may not even know just how bad it is. Fortunately, there are tools that can help.
To evaluate the current state of your Active Directory groups, take a look at Imanami’s free GroupID Health Meter diagnostic tool to evaluate the strengths and weaknesses of your Active Directory group management.
A Healthy Active Directory Makes for a Healthy Environment
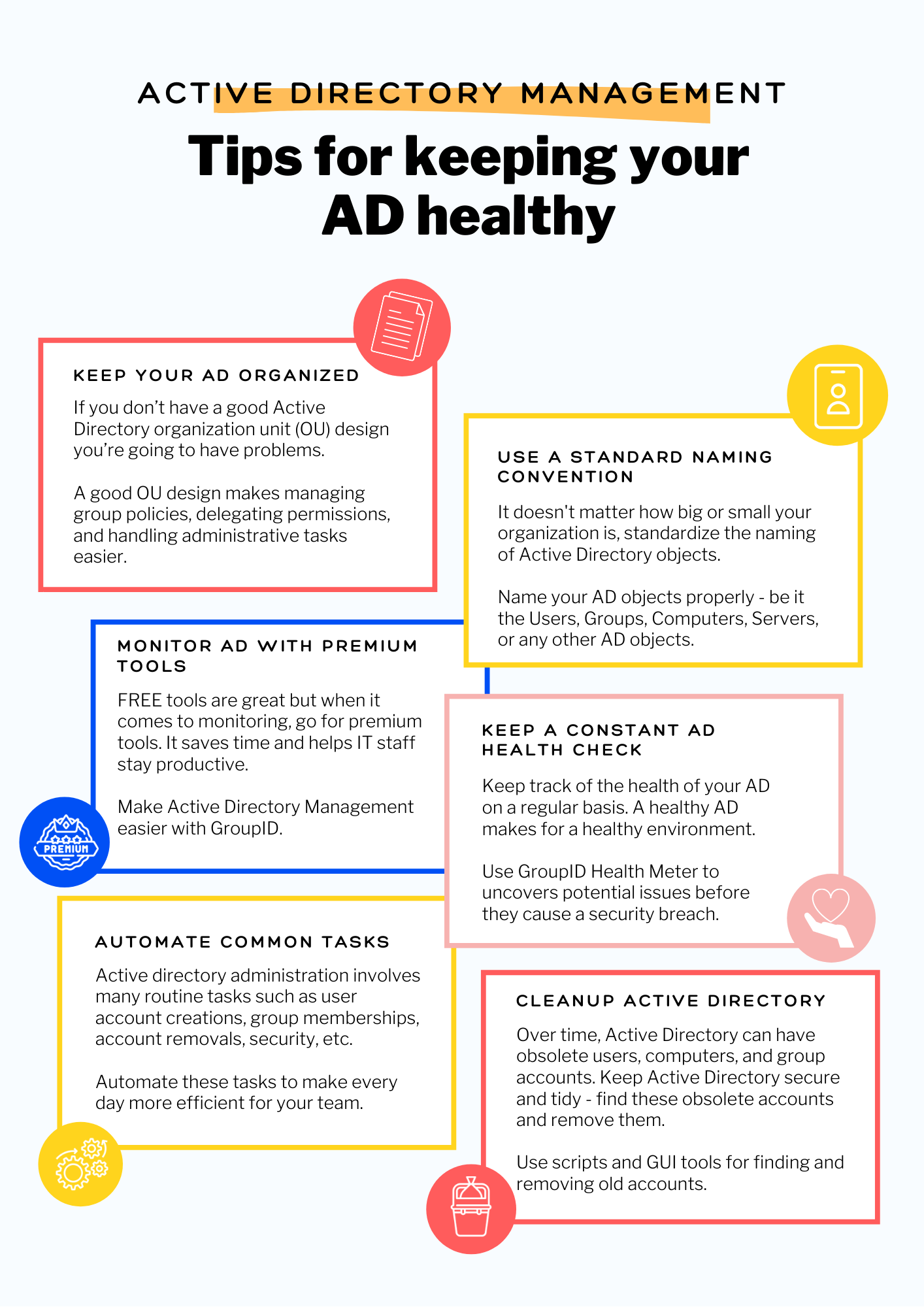
If you already have an idea of how bad the state of your Active Directory group management may be, there are resources to help you, too. Our mission here at Imanami is to help you kick those bad habits. Let us help. The health of your Active Directory groups may depend on it. We have listed some effective tips to help you get started in the image below.
Read more: Make Active Directory Group Management Easier
For more information on how to properly manage Active Directory groups, check out our whitepaper on 7 Best Practices to Better AD Group Management.
GroupID by Imanami offers a suite of solutions that empowers IT professionals to manage groups, users, and entitlements effectively and automatically. Learn more about the suite of solutions under GroupID here.
Jonathan Blackwell
View ProfileSince 2012, Jonathan Blackwell, an engineer and innovator, has provided engineering leadership that has put GroupID at the forefront of group and user management for Active Directory and Azure AD environments. His experience in development, marketing, and sales allows Jonathan to fully understand the Identity market and how buyers think.