Issue with Query Based Distribution Groups and BPOS
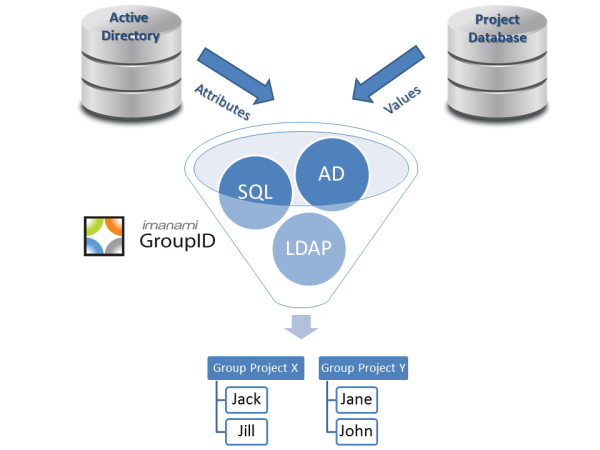
Somehow I missed a comment that was posted on a previous blog post titled An alternative to Query Based Distribution Lists (QBDLs). In that post, I was talking about the advantages of actually creating a group in Active Directory with your queries vs. the QBDL method of executing the query against Active Directory every single time…