Running in Circles: Circular Group References in Active Directory
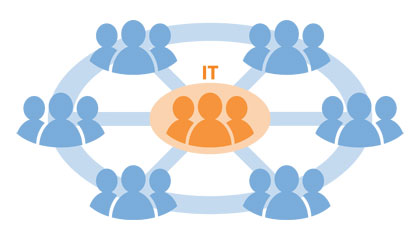
Who’s in charge here, anyway? Even if you have only a modicum of proper group management in place, your groups should at very least have some documentation of (a) how a given group is being used in the Notes field and (b) who is responsible for the group in the Managed By field, for the…